Optical Switching
To a casual
observer of the networking industry around the year 2000, it might have
appeared that the most interesting sort of switching was optical switching.
Indeed, optical switching did become an important technology in the late 1990s,
due to a confluence of several factors. One factor was the commercial
availability of dense wavelength division multiplexing (DWDM) equipment, which
makes it possible to send a great deal of information down a single fiber by transmitting
on a large number of optical wavelengths (or colors) at once. Thus, for
example, you might send data on 100 or more different wavelengths, and each
wavelength might carry as much as 10 Gbps of data.
 |
| Optical Switching |
A second
factor was the commercial availability of optical amplifiers. Optical signals
are attenuated as they pass through fiber, and after some distance (about 40 km
or so) they need to be made stronger in some way. Before optical amplifiers, it
was necessary to place repeaters in
the path to recover the optical signal, convert it to a digital electronic
signal, and then convert it back to optical again. Before you could get the data into a repeater, you would have
to demultiplex it using a DWDM terminal. Thus, a large number of DWDMterminals
would be needed just to drive a single fiber pair for a long distance. Optical
amplifiers, unlike repeaters, are analog devices
that boost whatever signal is sent along the fiber, even if it is sent on a
hundred different wavelengths. Optical amplifiers therefore made DWDM gear much
more attractive, because now a pair of DWDM terminals could talk to each other when
separated by a distance of hundreds of kilometers. Furthermore, you could even
upgrade the DWDM gear at the ends without touching the optical amplifiers in the
middle of the path, because they will amplify 100 wavelengths as easily as 50
wavelengths.
With DWDM and
optical amplifiers, it became possible to build optical networks of huge
capacity. But at least one more type of device is needed to make these networks
useful—the opti- cal
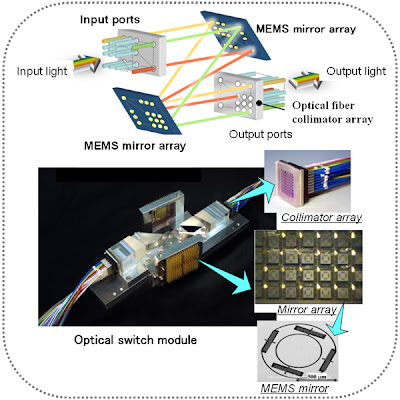
switch. Most so-called optical switches today
actually perform their switching function electronically, and from an
architectural point of view they have more in common with the circuit switches of
the telephone network than the packet switches described in next post. A
typical optical switch has a large number of interfaces that understand SONET
framing and is able to cross-connect a SONET channel from an incoming interface
to an outgoing interface. Thus, with an optical switch, it becomes possible to
provide SONET channels from point A to point B via point C even if there is no
direct fiber path from A to B—there just needs to be a path from A to C, a
switch at C, and a path from C to B. In this respect, an optical switch bears
some relationship to the switches, in that it creates the illusion of a
connetion between two points even when there is no direct physical connection
between them. However, optical switches do not provide virtual circuits; they
provide “real” circuits (e.g., a SONET channel). There are even some newer
types of optical switches that use microscopic mirrors to deflect all the light
from one switch port to another, so that there could be an uninterrupted optical
channel from point A to point B. We don’t cover optical networking extensively
in this book, in part because of space considerations. For many practical purposes,
you can think of optical networks as a piece of the infrastructure that enables
telephone companies to provide SONET links or other types of circuits where and
when you need them. However, it is worth noting that many of the technologies that
are discussed later in this book, such as routing protocols and Multiprotocol
Label Switching, do have application to the world of optical networking.